Please read this article to learn how to protect your Parallels account from unauthorised access from unknown devices and locations using two-step verification.
Information
Two-step verification adds an extra level of security to your Parallels account. After two-step verification is configured for your account, you will sign in to it in two steps:
Step 1 – sign in using either your Parallels account credentials (email and password) or external service (Apple, Google, or Facebook).
Step 2 – depending on the preferred verification method configured in your account: either use the link sent to your account email address to confirm that you trust the web browser or mobile device from which the login attempt is being made; or confirm the login by entering the one-time password created by the authenticator app installed on your mobile device and registered in your account.
Access to your account is granted when both steps are completed successfully.
To enable two-step verification:
- Use a web browser to sign in to your Parallels account at https://my.parallels.com
- Open the Security Settings page (https://my.parallels.com/profile/personal/security)
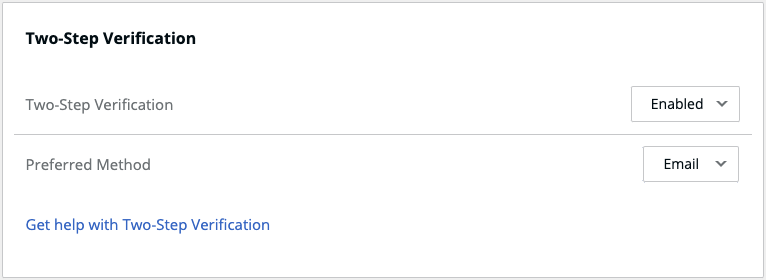
- Switch the Two-Step Verification option to Enabled
Select the Preferred Verification Method
Choose ‘Email’ to approve logins to your account via email. Each time you sign in to your Parallels account from an unknown browser or mobile device, you will receive a message from Parallels where you need to confirm that you trust this browser or device.
IMPORTANT! - before you confirm, please carefully check the origin of the request – name/type of the browser, IP address/location, and time of login attempt.
Alternatively, choose ‘Authenticator app’ if you want to confirm logins to your account by entering a one-time password generated by the authenticator app installed on your mobile device. You will have to install one of the recommended authenticator apps (e.g., Google Authenticator or Microsoft Authenticator) on your iOS or Android device and register it with your Parallels account. Once the authenticator app is configured, you will have to confirm login to your account by entering a one-time password generated by your authenticator app.
Was this article helpful?
Tell us how we can improve it.