Symptoms
Some users are not able to login using Radius MFA based on the Network Policy Server with the following error:

Cause
On Active Directory Users and Computers > find the affected user account > Properties > Dial-in:
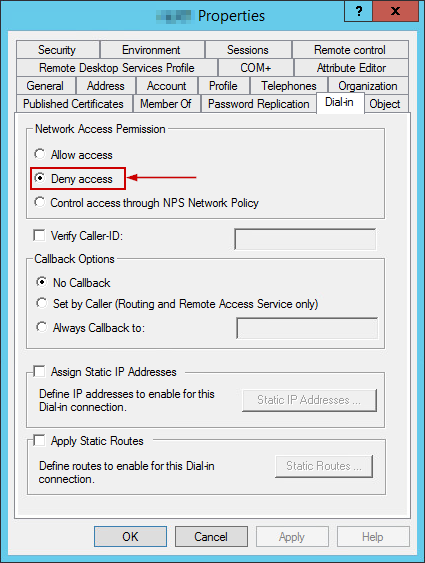
When it's set to Deny Access, authentication with NPS-based MFA solutions will not be usable.
Resolution
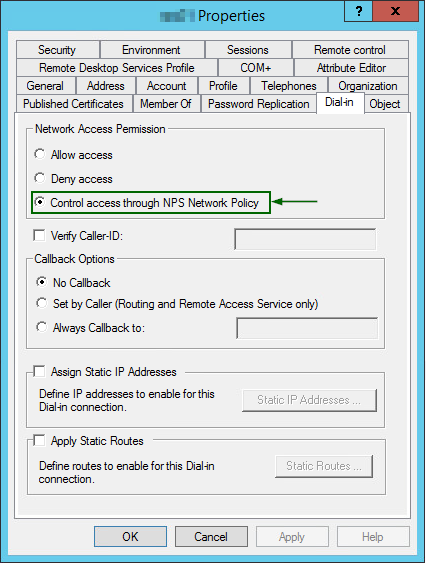
NOTE: The Allow Access setting is almost equal to bypassing any checks from the NPS side so it can be used for testing purposes only. It is not recommended to use this option in production as it increases security risks.
1. Switch it back to the default option - Control access through NPS Network Policy:
2. Ensure that Network Policy is configured correctly on NPS. Here is an example:

3. If the policy is already created, open properties for this policy and compare to this example:
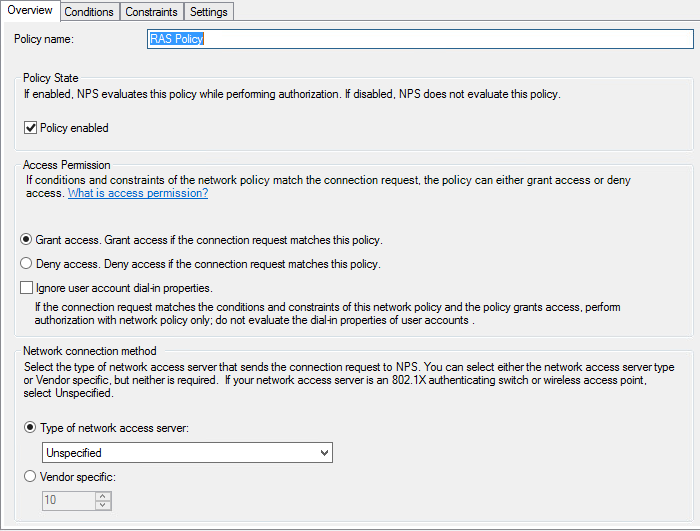
4. Configure Conditions tab:

5. Set authentication methods in Constraints tab:

6. At the Settings tab, keep defaults unless you are familiar with the effects of any setting change in there.
7. Click Apply and OK.
At this point, the adjusted Network Policy should be granted access to users and they should be prompted for OTP and get push notifications, SMS, or email codes depending on the MFA solution configurations.
Was this article helpful?
Tell us how we can improve it.