Symptoms
I would like to restrict Parallels Client users from accessing Terminal Servers through Native RDP.
Cause
In order to be able to launch published applications users have to be added to "Remote Desktop Users" group. This will allow users to access Terminal Servers using Native RDP.
Resolution
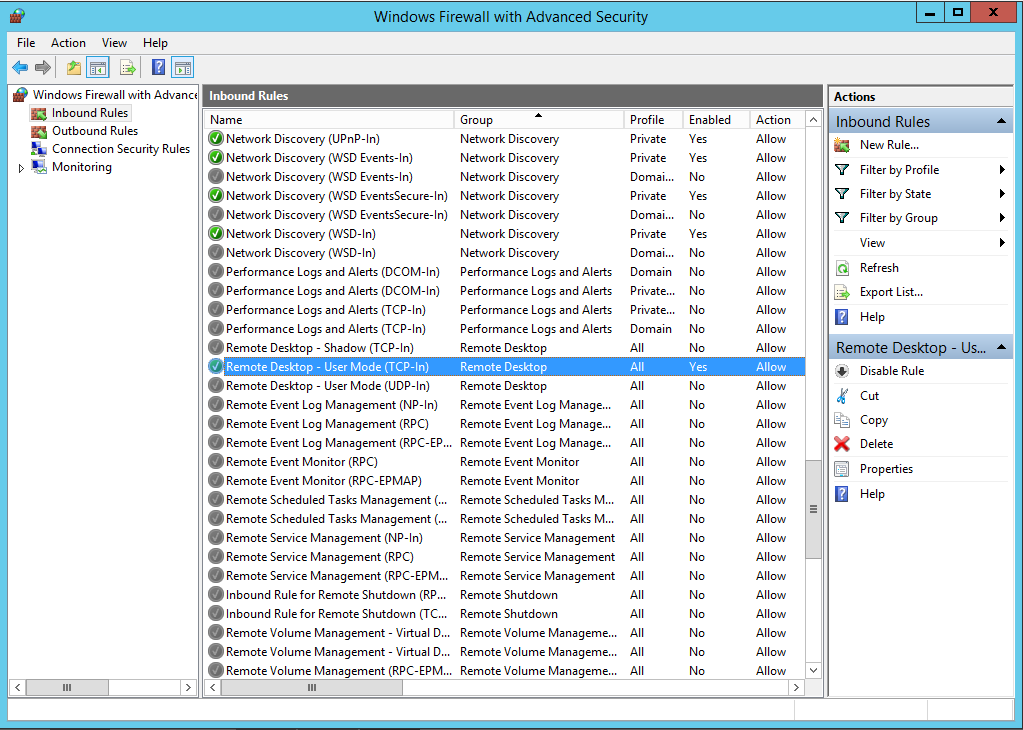
Such restrictions are possible to be made using Windows Firewall with Advanced Settings.
-
Navigate to the Terminal Server and access Windows Firewall with Advanced Settings
- Highlight Inbound Rules and locate inbound rule for Remote Desktop connections
-
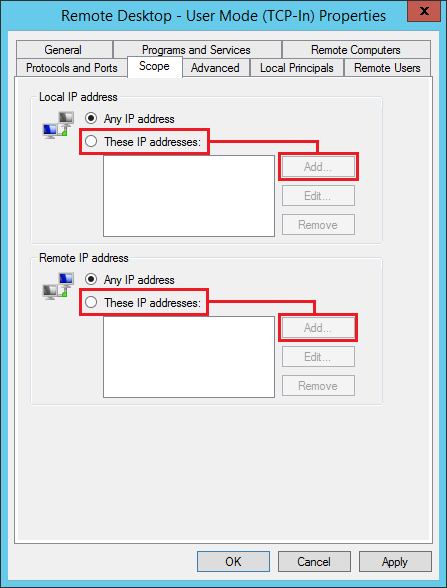
Right-click this rule and select Properties.
-
In opened window navigate to "Scope" tab.
- Depending on the location of Remote Application Server Gateway select "These IP addresses" checkpoint either in "Local IP address" or in "Remote IP addresses" field and click "Add" button. (The choice should depend on if the Gateway Server is located in internal or external network)
- After clicking "Add" button one will be prompted to specify the exact IP addresses from which RDP connection to this Terminal Server will be possible. Please type the IP address of Remote Appication Server Gateway and press "OK" button. In case if your RAS Environment have multiple Gateways please specify IP Addresses of all Gateway Servers
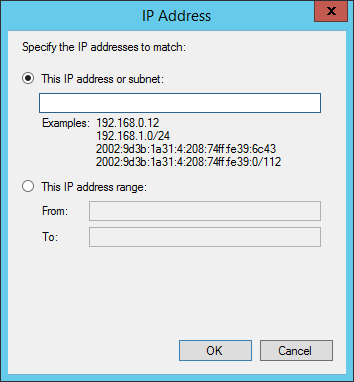
- Click "OK" button and Apply setting changes.
Applying this settings to inbound rule for RDP Connection will restrict users from direct access to this terminal server, however will allow Parallels Client users to launch applications published from this server.
PLEASE NOTE: If such changes will be implemented - only users who use Gateway connection mode in Parallels Client will be able to launch published applications.
Was this article helpful?
Tell us how we can improve it.